Introduction to lab #
This lab project introduces provide hands-on experience in IT and cybersecurity. The series will cover building a network, breaking it with penetration tests, and then monitoring and defending against those attacks, all within a safe, controlled environment.
Lab Scenario and Topology: The lab is built around a fictional company, that needs its IT infrastructure. Key issues to be addressed include:
- Lack of centralized resources, file shares, storage, backups, and security.
- No user management.
- Disorganized network with uncontrolled device connections.
- Concerns about ransomware attacks and a desire for hardened, monitored, and defensible systems.
- Hands-on Experience: You will gain practical skills in building networks, dealing with virtual machines, and administering systems.
- Safe Environment: It provides a safe and controlled environment to learn how to break and defend systems without causing real-world damage.
- Comprehensive Skill Set: By the end of the series, you will learn how to harden systems, conduct penetration testing (red teaming), and perform threat monitoring and analysis (blue teaming).
- Industry Preparation: The skills taught, such as configuring firewalls, Active Directory, and DNS, are directly applicable to real-life industry scenarios.
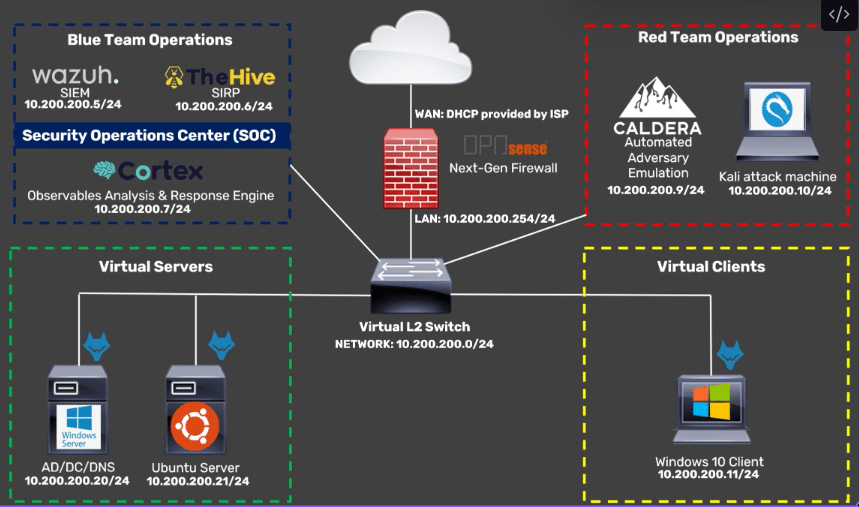
The proposed network topology includes:
- Virtual Servers:
- Email server
- Windows Server for Active Directory, Domain Controller, DNS, and file shares
- Ubuntu Server for various services and tool testing
- Elasticsearch stack for system monitoring and logging
- Networking and Security:
- Opnsense Next-Generation Firewall with Sensei feature extensions
- Virtual Clients:
- Windows 10 client for testing
- Kali attack machine for launching attacks
- All devices will be connected to a virtual layer 2 switch and virtualized using VirtualBox or other hypervisors like Hyper-V or VMWare. Future plans may include cloud integration and additional branch sites.
Key Learning Outcomes: By the end of the series, you will gain skills in:
- Basic network configurations.
- Configuring firewalls, servers, Active Directory, DNS, and user management.
- Hands-on Windows and Linux server and client administration.
- Hardening devices and networks.
- Exposure to penetration testing tools and techniques.
- Hands-on experience with blue team monitoring and defense against attacks.
All the best 🙂
