Now that we are familiar with the Cyber Kill Chain and its stages, we can better predict and anticipate the next steps in an attack and also suggest appropriate measures against them.
Just like the Cyber Kill Chain, there are different stages when responding to an incident, defined as the Incident Handling Process. The Incident Handling Process defines a capability for organizations to prepare, detect, and respond to malicious events. Note that this process is suited for responding to IT security events, but its stages do not correspond to the stages of the Cyber Kill Chain in a one-to-one manner.
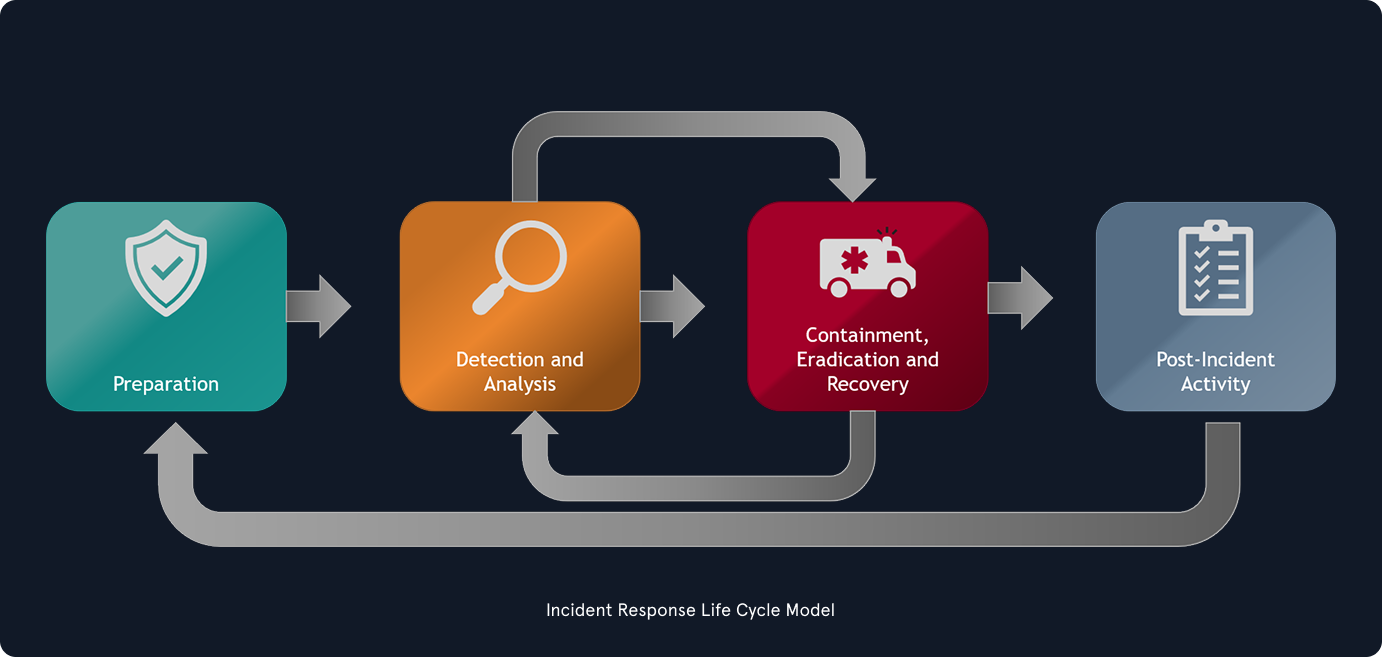
As defined by NIST, the incident handling process consists of the following four distinct stages:
Incident handlers spend most of their time in the first two stages, preparation and detection and analysis. This is where we, as incident handlers, spend much time improving ourselves and looking for the next malicious event. When a malicious event is detected, we move on to the next stage and respond to the event (but there should always be resources operating in the first two stages, so there is no disruption of preparation and detection capabilities). As we can see in the image, the process is not linear but cyclic. The main point to understand at this stage is that as new evidence is discovered, the next steps may also change. It is vital to ensure that we don’t skip steps in the process and that we complete a step before moving on to the next one. For example, if we discover ten infected machines, we should certainly not proceed with containing just five of them and starting eradication while the remaining five stay in an infected state. Such an approach can be ineffective because, at the bare minimum, we are notifying an attacker that we have discovered them and that we are hunting them down, which, as we can imagine, can have unpredictable consequences.
So, incident handling has two main activities, which are investigating and recovering. The investigation aims to:
Discoverthe initial ‘patient zero‘ victim and create an ongoing (if still active) incident timeline.- Determine which
toolsand malware the adversary used. Documentthe compromised systems and what the adversary has done.
Following the investigation, the recovery activity involves creating and implementing a recovery plan. Once the plan is implemented, the business should resume normal operations, if the incident caused any disruptions.